
[responsivevoice_button]
From some weeks group of hackers are breaking into the people’s routers and hence changing their DNS setting to point their devices to fake coronavirus themed pages malware. According to cybersecurity researcher firm Bleeping Computers and Bitdefender, the attackers are currently targetting D-Link and Linksys routers.
It seems that attackers are finding vulnerable routers on the internet and brute-forcing the default admin and password and further changing their DNS settings to redirect them to a fake page that was created by the attackers.
DNS( Domain Name Setting) is the gateway that converts the domain names into IP addresses.
Hackers are targeting some of the most common URL listed below
- “aws.amazon.com”
- “goo.gl”
- “bit.ly”
- “washington.edu”
- “ufl.edu”
- “redditblog.com”
- “disney.com”
- “cox.net”
- “xhamster.com”
- “tidd.ly”
- “fiddler2.com”
- “winimage.com”
- “pubads.g.doubleclick.net”
- “imageshack.us”
After that, the attackers redirect the above-listed domain names to 176.113.81.159, 193.178.169.148, 95.216.164.181 the following IP which shows a fake pop-up from the World Health Organization telling them to download and install an app that would display information and instruction about the COVID-19.
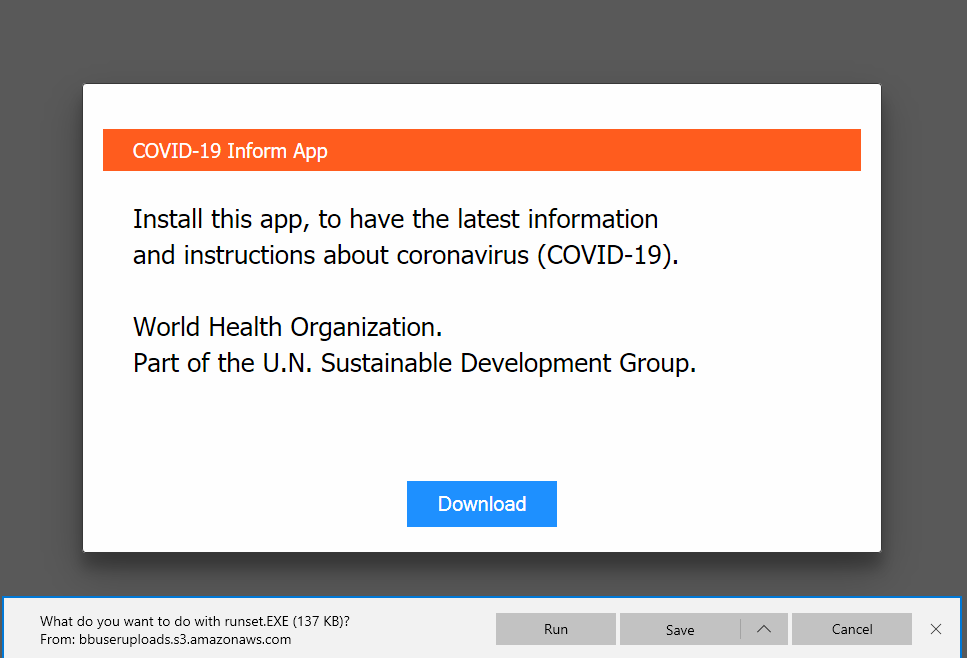
If a person who does not have technical knowledge will easily believe that it’s a legitimate website because of the domain name remain unchanged and seems to appear legitimate.
As soon as attackers click on the download button he/she is redirected to a fake malicious website to make sure that the victim doesn’t suspect the foul play the attackers also use the famous URL shorteners to hide the malicious URL.
After downloading the COVID-19 information application which is an Information Stealer Malware ” Oski information-stealing” that is when launched will capture the following information
- saved login credentials
- cryptocurrency wallets
- text files
- browser form autofill information
- Authy 2FA authenticator databases
- browser history
- a screenshot of your desktop at the time of infection
- browser cookies
- browser payment information, and more.
Here are two malicious DNS that are used by attackers 109.234.35.230 and 94.103.82.249.
How to spot this attack and fix it
- Login into your router
- Locate the DNS setting tab and check that there are no manually configured DNS especially 94.103.82.249
- and 109.234.35.230. If you are having some doubt set the DNS to automatic configure or the ISP provided.
- Use strong admin password so that attacker cannot brute-force the credentials
- Apply all the latest patch available







