
A new vulnerability in Google Play Core Library was published in late August that could allow Local-Code-Execution (LCE) in the scope of any Android App that uses the vulnerable version of Google Play Core Library.
The vulnerability could allow an attacker to execute arbitrary code in the Android apps that use the vulnerable version of the Core Library.
According to the Google, Developers Core Library is your app’s runtime interface with the Google Play Store. Some of the things you can do with Play Core include the following:
- Download additional language resources
- Manage the delivery of feature modules
- Manage the delivery of asset packs
- Trigger in-app updates
- Request in-app reviews
Google Play Core Library Vulnerability
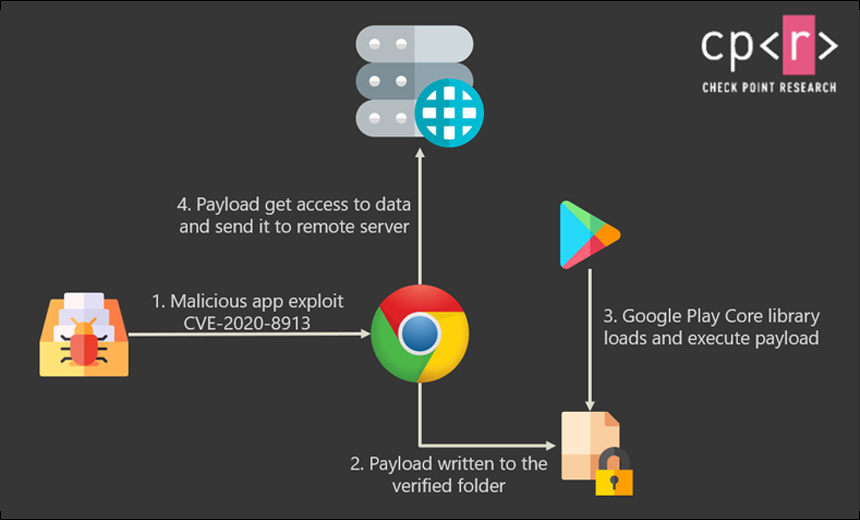
The vulnerability can be tracked as CVE-2020-8913, the core library vulnerability is an arbitrary code execution vulnerability that existed in the SplitCompat.install endpoint in Android’s Play Core Library versions prior to 1.7.2.
A malicious attacker can create a malicious Apk to target a specific application and on successful execution, the attacker can perform directory traversal, execute code on the Android App.
Moreover, On successful execution of the vulnerability, it can have severe high risks, an attacker can inject code into banking applications to grab credentials, Inject code into Enterprise applications, Inject code into social media applications.
However, the Google Play core library vulnerability patched by Google on April 6, 2020. But why is more left now?
Read Also: Top 5 Coding Apps for Android You Need
Why to care about it?
However, the vulnerability has patched by it also needs to be pushed by the developers into Google.







