
[responsivevoice_button]
A very cleverly managed Android hacking campaign infecting smartphones and running over the years, which gives the operators of the malware full control over the device and completely hidden in the devices from the users.
Mandrake spyware abuses the functionality of the Android that lets attackers take full control over the compromised device and access all the data of the victims.
Mandrake malware is capable of sending all the SMS, stealing Credential stealing of any account, Screen recording, taking screenshots of the device, initiate a factory data reset to remove all the traces of the malware, and sending all the data from victims device to the servers.
A detailed report about the malware has been published by the researchers at Bitdefender about the Mandrake Android malware. Mandrake malware gains the administrative privileges which ensure that it cannot be uninstalled until this privilege is removed.
The estimate says that the number of victims is in tens of thousands for the current wave, and probably hundreds of thousands throughout the full 4-year period
Bitdefender researchers said.
The attackers have also planted a kill switch in the Mandrake malware that can wipe out the traces from the compromised devices.
Technique used by Mandrake’s malware
Mandrake’s developers had put serious efforts to make it hidden over the years the developers maintain several applications onto the Play Store under the name different other developers. However, all the applications have been removed from the Play Store.
Also, the applications were mostly ad-free to make the users happy and also the developers pay attention to negative reviews and often deliver fixes for issues reported by users.
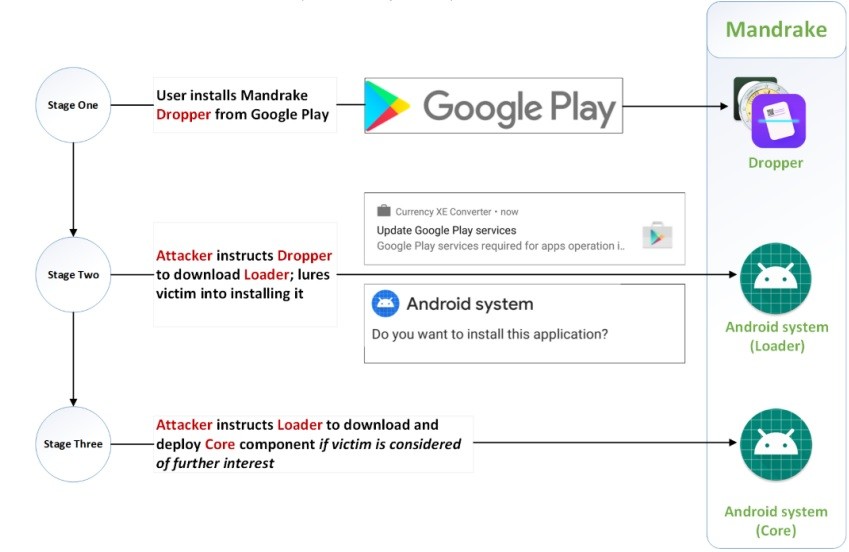
Also, the malware uses multi-stage processes to hide the payload and avoid the detection by Google Play. After the application is installed in the user’s device it contacts the command and control server and downloads the loader that provides Mandrake with the capability to take control over the device.

During the initial stage, there is no suspicious activity found on after that the malware downloads the loader and in the second stage, the loader downloads the base for the core components, and if the attackers choose it downloads the core components and fully take over the device.
The malware also avoids running on the devices with no SIM cards or with SIMs issued by specific operators.







