Russian based hacking group named Turla used malware, a downloader, and a backdoor in a waterhole operation. This Russian based hacking group have compromised at least four websites of which two were Armenian government.
Waterhole attack is a strategic attack in which attacker infects the website which is often visited by the victim or particular targetted groups.
The strategy behind the attack
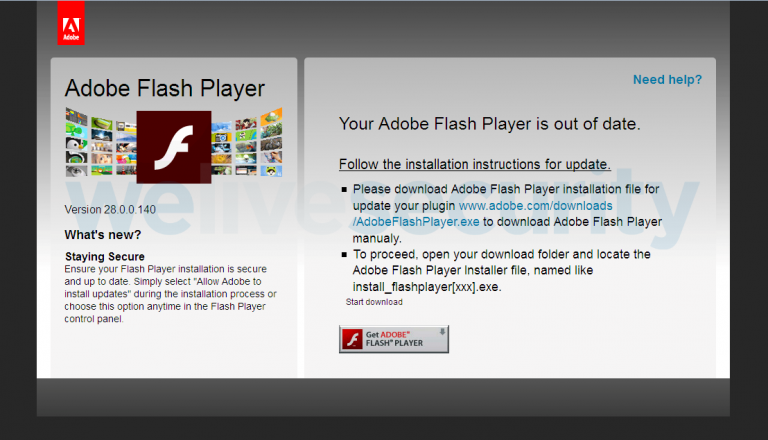
The tools used by hackers were a .NET malware dropper named NetFlash and a backdoor scripted in python named as PyFlash. The attackers had made a fake Adobe Flash update to the victims.
After successfully taking control over websites the attacker plays a tricky game without knowing the users they inject a persistent cookie script the source code is available on Github and malicious Javascript code that is embedded on a Chinese website named “skategirlchina(.)com” which is designed to fingerprint the visitor’s web browsers and the cookie code was to track the future visits of the victim.
From there hackers collect necessary information like OS info, screen recording and many more and sends a POST request to the C&C server. If the user clicks on the fake Flash Player update iFrame created by malicious JavaScript original Flash Player and Turla malware both get installed at same.
Tools used in Turla Malware
NetFlash (.NET downloader)
The NET application drops and Adobe Flash v32, and NetFlash (a .NET downloader) after that the next stage for the attack begins and NetFlash starts second stage malware from a hardcoded URL to remain its persistency.
PyFlash
A py2exe backdoor is executed and converts it into a Python script Windows executable. The backdoor communication was done with C&C server via HTTP request and whole communication was encrypted with an AES key and this sends various information related to the system like IP, mac address, system-info, task list etc..
Samples and other information related to C&C server has been mentioned by We Live Security








