
M2 smartwatch by Chinese company SMA has major security issues in the back-end of their mobile app that connects with the cheap $35 smartwatch.
The smartwatch works on a GPS tracking system. A Sim-Card is inserted in the watch that tracks the live location of children.
In a report by the IoT lab of the AV-test Institute, Researchers claimed that the back-end can be easily queried via a public accessible Web-API. A brute-force attack is enough to get into the data of over 5,000 children. The API is the same as that shows data on parents’ smartphones. The API can reveal details such as images, registered address data, IMEI code of the clock modem.
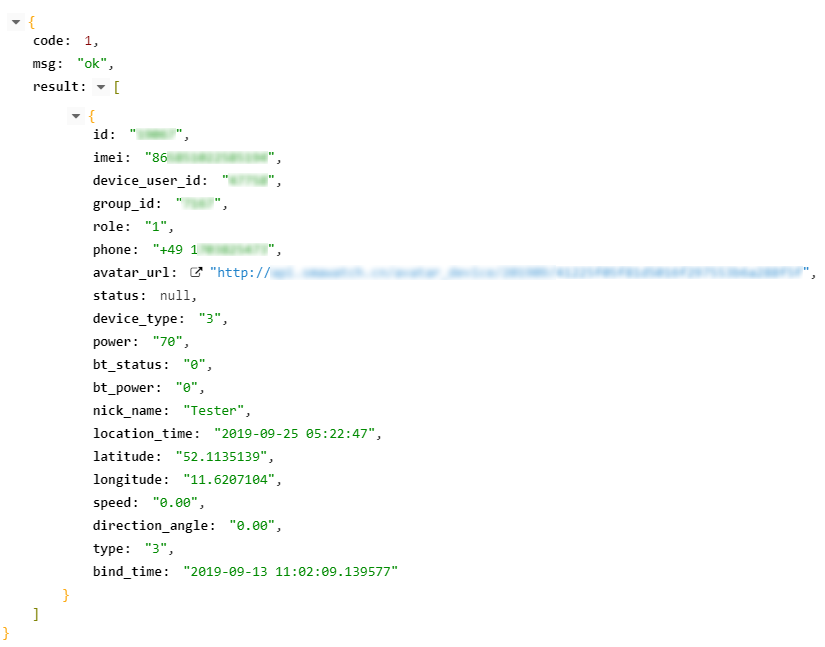
Attackers are given access to sensitive personal information, including the name of parents, the name and image of the child, names and numbers of relatives and acquaintances in the phone book that can be used in the event of possible contact with the child.
Maik Morgenstern, AV-Test Lab
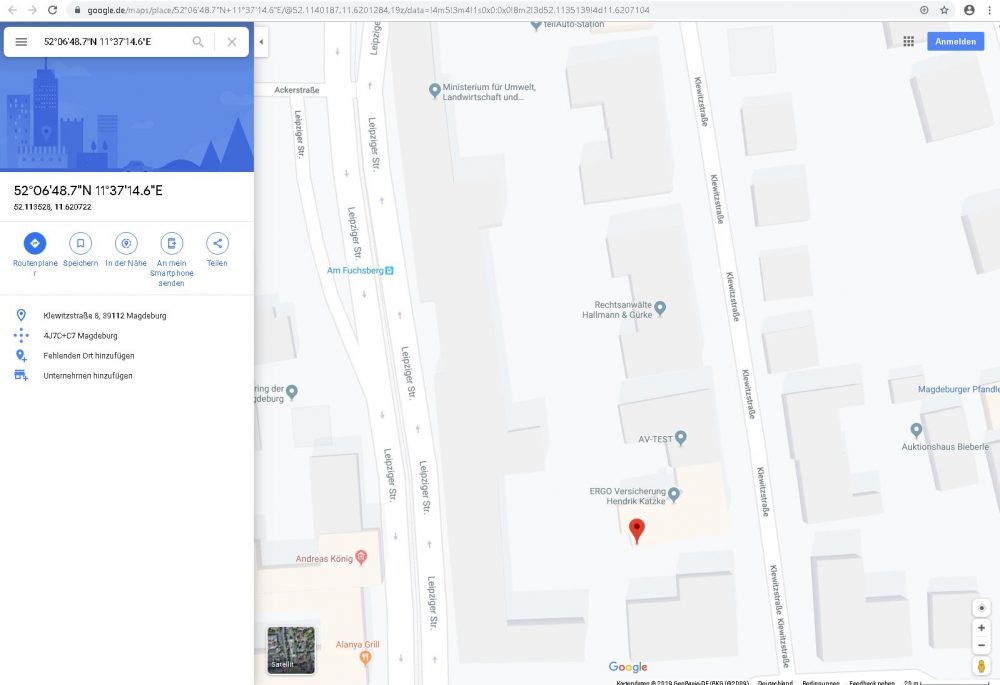
Position determination, voice messages and several other functions of the smartwatch can also be accessed by the vulnerability. Data from over 10,000 parents account can be accessible by potential attackers. The accounts accessible include children of the countries — China, Hong Kong, Spain, Turkey, Poland, Netherlands, Mexico, and Belgium.







