
What is a Ransomware?
Ransomware is a type of malicious software(i.e “malware” in short) that is used by cybercriminals to hold people or big organizations. And as a result, cybercriminals threaten these normal people or organizations to pay a ransom in order to regain access to their computer or data.
Types of Ransomware:
There are mainly two types of Ransomware:
- Crypto Ransomware: Crypto Ransomware encrypts important files on a computer so that infected victims cannot access them and demands a ransom from them if they want to get their files back.
- Locker Ransomware: Locker Ransomware does not encrypt files and rather locks the victim from using their device. After they are locked out, the cybercriminals ask for a ransom to unlock the device.
What to do after a ransomware attack?
1. Ignore the demand for Ransom
Keep this in mind, never ever try to pay the ransom. According to research, it shows that more than 60% of the victims, pay the ransom, and not even get their data back. So, it is better not to surpass the money in the hands of the criminal gangs as it will encourage them to perform their illegal activities again and again.
2. Remove the Ransomware from the Computer
Ransomware may appear threatening and another form of malware. There are companies that provide low-cost ransomware and phishing tools, or malware removal tools including Microsoft and Bitdefender.
Both of the sites provide instructions on how to eliminate ransomware from your computer. It’s best to remove the malware as soon as possible as you are giving them the opportunity and time to spread the malware by encrypting files on the system further and potentially spreading to other computers connect to the network as well.
3. Update the Antivirus and patch your OS
If your current antivirus protections let the ransomware get into your computer, then either the antivirus is corrupted, or perhaps it is not being updated regularly with the latest security patches. Also, If you want to protect your computer in the future properly then you need to keep advanced antivirus running and up to date. If your software isn’t up to date either update it immediately or replace it with the new one which provides adequate security support. Once you have your antivirus ready, it’s always good to scan your device first to make sure that no further problems or security threats that exist in your system.
4. Update your Passwords
Once you gain access to your computer make sure you change the password that you use to access websites or other devices. If your antivirus protection breached, you may have no idea what information has been taken down. So the best and safest approach is to change all the passwords and then monitor your accounts for any indications of suspicious activities or vulnerabilities.
5. Back up your files
If your system gets infected with ransomware it is most likely that you are either not going to get it back or may receive it with some damage or data loss. So, the best preventive measure is to regularly back up your files on an external system(mainly a hard drive or you may store it in the cloud-or both), so if your data is under hostage, you can access it from another location. Keep in mind that your data is your responsibility, after all, no one is going to suffer more than you yourself.
6. Train yourself to Recognize Phishing Attacks
Phishing Attacks use social engineering tricks and tempt employees or certain individuals to click on malicious links, and this is the number one way that ransomware gets into the system. The first attempt is to train people on what to look for, what to avoid, and how to identify suspicious emails. In 2020, due to the remote working for the COVID-19 situation, people have been more vulnerable to these attacks.
The 5 Most Dangerous Ransomware Attacks:
1. Maze Ransomware
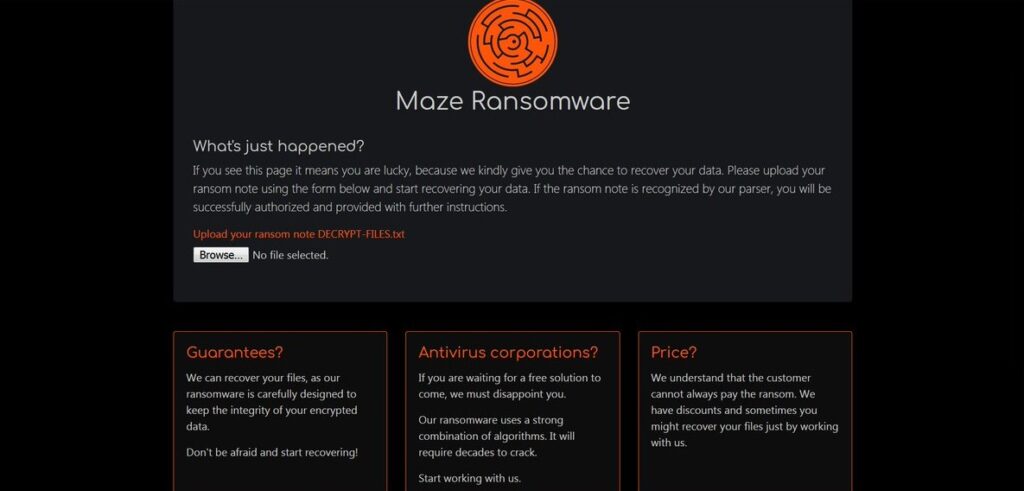
This ransomware was discovered by Jerome Segura on May 29, 2019, and is the most infamous threat to enterprises all over the world. Previously, it was known as “ChaCha ransomware”. This hacking community used exploit kits like Fallout and Spelvo to deploy attacks.
The ruthless ransomware is infamous for its new approach of its attacking where it publishes sensitive information publicly and then it encrypts the files and demands for ransom. It threatens the victim with the word that it will release the information publicly on the internet if they don’t pay the ransom on time. Actually, the threatening makes no sense, as all the files are already available on the internet. Their most recent victims are Cognizant, Xerox, and healthcare industries.
2. REvil Ransomware
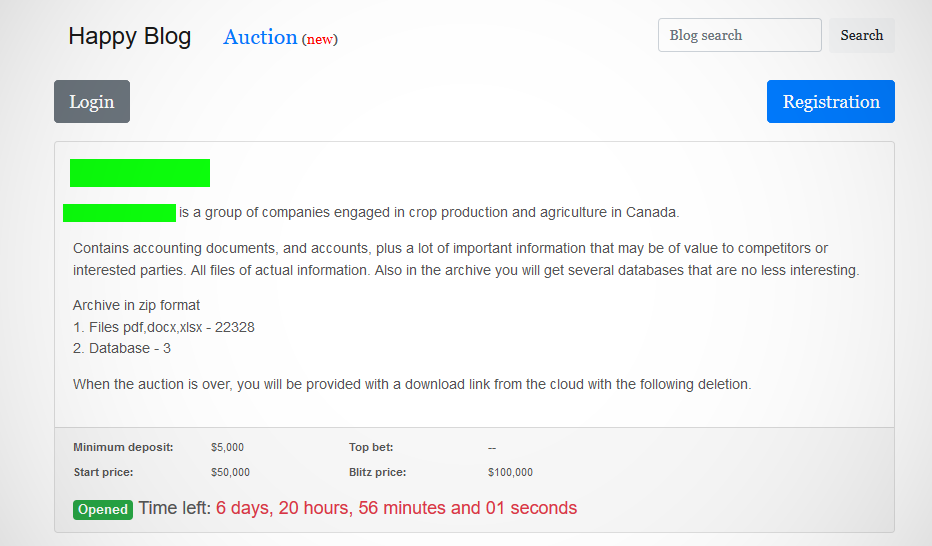
The REvil ransomware made headlines in the news for the latest data breach on the media and entertainment lawyers. This ransomware is mainly a file blocking virus that encrypts the victim’s files after infecting the system with malware and then sends a request message. The request message asks for a ransom in the form of bitcoin. If the victim fails, then the demand is doubled.
The ransomware targeted many A-list celebrities and their law clients and leaked their data on the dark web. A series of screenshots including a legal document of Madonna’s tour contract and dozens of computer files of celebrities like Bette Midler, Barbra Streisand leaked on the dark web. According to reports, even personal info of stars such as Robert De Niro, Drake, Maria Carey, Rod Stewart, and many several others have been compromised.
3. Ryuk Ransomware
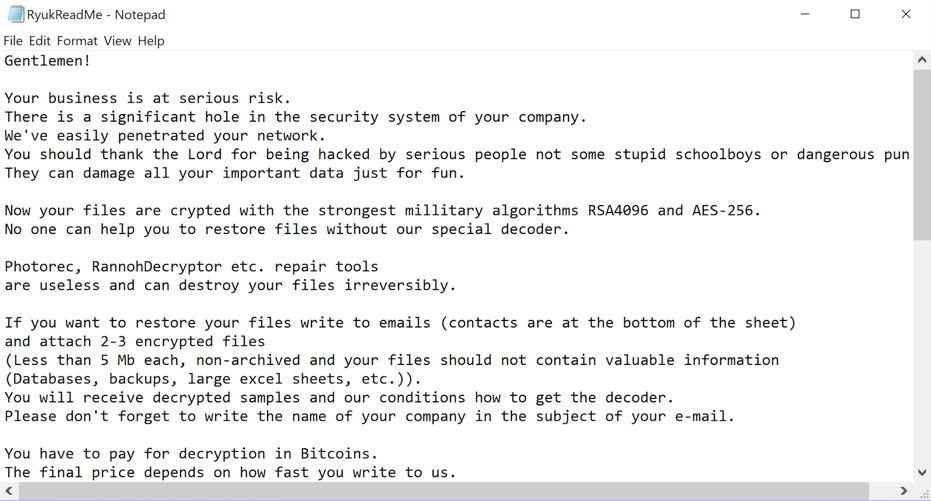
The Ryuk Ransomware is one of the active and the biggest players among the other ransomware. It is a type of crypto-ransomware which blocks access to a file and encrypts them and then demands the ransom.
Ryuk uses TrickBot or other Malwares to invade into the system. It also uses other means like Remote Desktop Services to gain unauthorized access into the systems. It uses robust military algorithms i.e. RSA and AES to encrypt files and set it up with a unique key for each executable.
Ryuk ransomware mainly targets business giants and government agencies that can pay huge ransoms. It recently targeted a US-based Fortune 500compny, EMCOR, and took down some of its IT systems.
4. Tycoon Ransomware
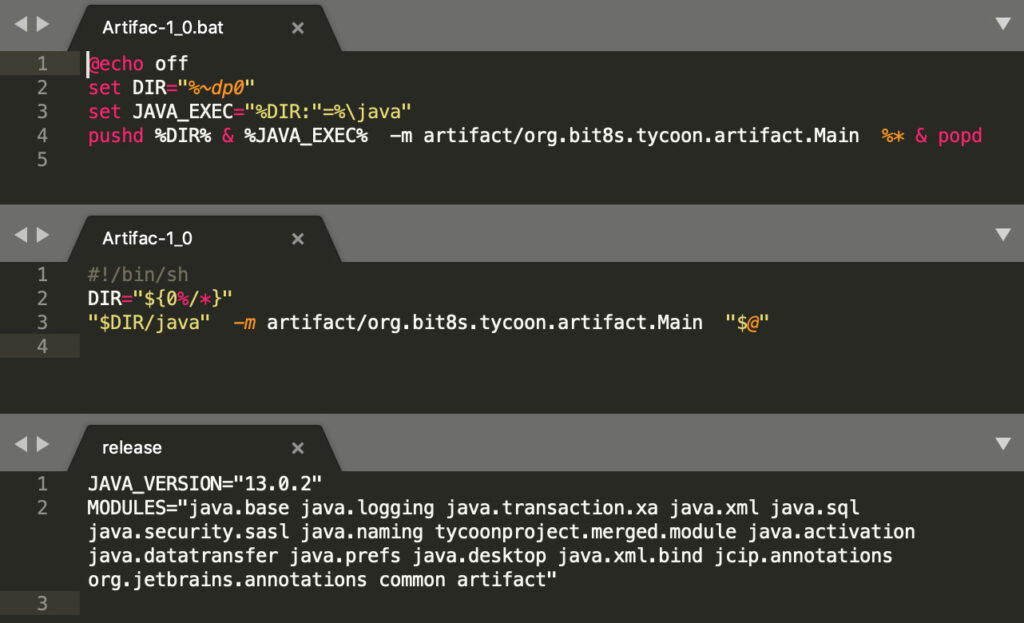
The Tycoon is written in Java and is a very recent and newly discovered ransomware. It has been targeting several organizations in the education and software industry. This malware is deployed in a trojanized version of Java RuntimeEnvironment and is compiled in ImageJ, a Java image format.
Tycoon uses different techniques to stay hidden across the globe. First of all, it denies access to the administrator and then infects the system with an attack on the files servers and domain controller. Tycoon heavily takes advantage of weak or compromised passwords and it exploits servers for malware.
5. NetWalker Ransomware
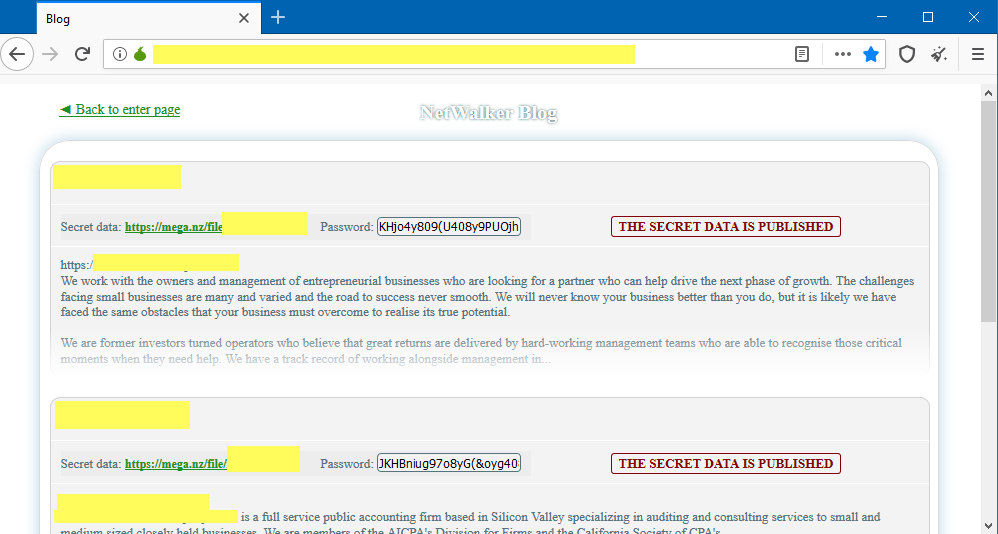
Mailto or NetWalker ransomware compromises the network of its victim and encrypts all the Windows devices running and that connects to the network. When executed, it uses an embedded config that includes file names, the ransom note, and several configuration options.
This is a new variant but a lot of individuals, enterprises, and healthcare organizations are found to affect by the same this year according to reports.
According to Security Researchers, Ransomware spreads mainly in two ways:
- Executable files that spread through networks
- Through phishing emails with a VBS script attached to the email







