
The InvisiMole hackers’ group has started a new campaign by revealing new toolset and collaboration with the advanced persistent threat (APT) group Gamaredon.
InvisiMole malware was the first time revealed in public by ESET in 2018 and InvisiMole malware was a complex malware and was capable of tracking the victim’s geographical location, spy via webcam, take screenshots, record audio, and steal documents.
These attacks were very few in numbers and were done on high-profile organizations in the military sector and diplomatic missions, both in Eastern Europe.
Updated Tools and Strategy
The recent version of the InvisiMole malware was using Media Transfer Protocol (MTP) that is capable to steal photos from mobile phones connected to the infected computer.
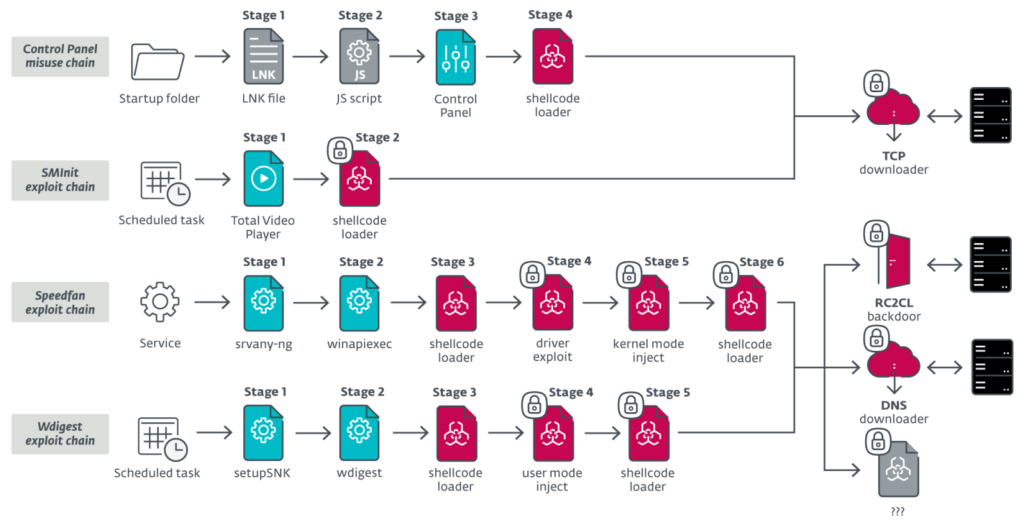
Researchers found that four execution chains were used according to the privilege level on the infected machine and version of the Windows installed in the targetted machine and the longest chain contains 6 steps.
The attackers also encrypted some of the payloads using the Data Protection API in Windows to encrypt and decrypt the payload. The Data Protection API is used in windows to protect login credentials and passwords and it can only be decrypted in the host.
The new InvisiMole malware also uses a new component that uses DNS tunneling for better communication with the C2 server. The researchers also noticed that InvisiMole also uses NSA EternalBlue (CVE-2019-0708) and BlueKeep (CVE-2017-0144).







