
New ransomware came into the eye of researchers named EKANS, aka ‘Snake Ransomware‘ written in Golang targets Windows user and encrypts system files and Volume Shadow Copies that the OS uses for backup.
Snake ransomware is a new type of ransomware that targets all the computers connected within the LAN. These enterprise targetting ransomware are used to infiltrate business networks, gather administrator credentials, and then use post-exploitation tools to encrypt the files on all of the computers on the same network.
The snake ransomware is first discovered by TheMalwaareHunter team and studied by Vitali Kremez, Head of SentinelLabs.
The ransomware contains a level of routine obfuscation not previously and typically seen coupled with the targeted approach,
Kremez, Head of SentinelLabs, told BleepingComputer in a conversation.
How does it work?

When started Snake, it starts removing computer’s Shadow Volume Copies and starts killing various processes like SCADA systems, virtual machines, remote management tools, network management software, and many more. It then starts encrypting various system files skipping some files listed below so that system boots normally.
- windir
- SystemDrive
- :\$Recycle.Bin
- :\ProgramData
- :\Users\All Users
- :\Program Files
- :\Local Settings
- :\Boot
- :\System Volume Information
- :\Recovery
- \AppData\
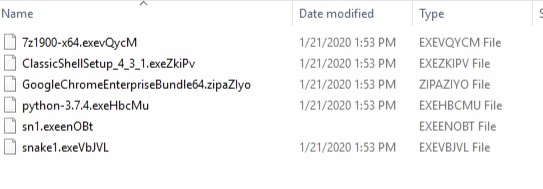
While encrypting a file, it appends some random A-5 character strings to a file extension making it more challenging to find the family of ransomware.
The attacker uses an encryption key of AES-256, RSA-2048, which makes it more difficult to extract the key and decrypt the files.
According to SentinelOne’s research, “If the threat is executed with administrative privileges, the ransom note will be written to c:\users\public\desktop\Fix-Your-Files.txt. If administrative privileges are not present, the ransom note will be written to an alternative location: c:\users\\AppData\Local\VirtualStore\.”
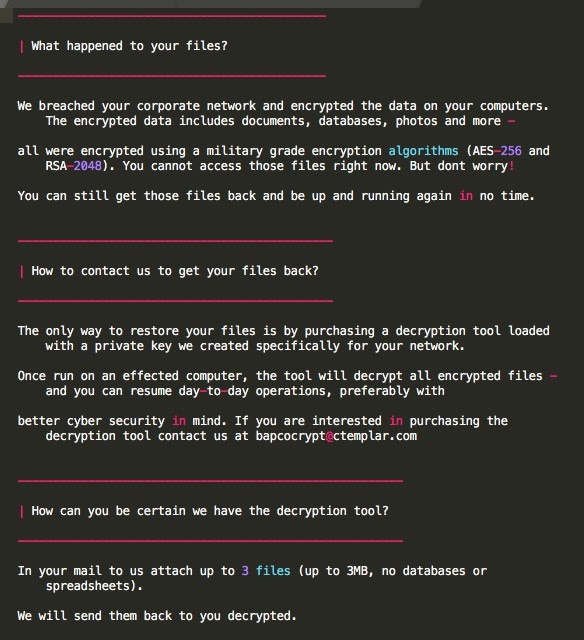
When the encryption process is completed, the ransomware drops a file named Fix-Your-Files.txt on Desktop, which contains the following note.
BeepingComputers said that they had tested much ransomware since 2013, but this ransomware took a long time to encrypt the files and tested on a small test machine as compared to other ransomware.
How to decrypt?
Although at that time it is currently, it doesn’t look very easy to find any recovery tool to decrypt the files. Since snake ransom can reinstall itself multiple times if you don’t remove core files, it is recommended to download Spy Hunter to detect its presence.
After removing core files of ransomware, try to restore files encrypted by snake ransomware by doing a system restore.







