
Local search service Justdial faced a security breach that exposed personal information of over 100 million users, an independent researcher has claimed. The informations include your address,mail id’s,names,phone numbers which could be possibly accessed from 2015 as the database and justdial’s application was not protected. And more over 70% of the exposed data were of the customers who just called the company’s famed customer care number 8888888888.The company denied the breach by saying that most of the APIs are foolproof and its current app doesn’t have any vulnerabilities.

JUSTDIAL is a company that provides local search for different services in India over voice calls and Internet.It’s core business is local search services.Its direct competitiors include companies such as Zomato and Practo. Justdial has stated that its exposure to any particular category is not more than 2-3% and it has not seen an impact on categories like doctors or on-demand services. Justdial Social, stylised as Jdsocial, is a service that aggregates content from social media websites, TV broadcast, news and other sources.
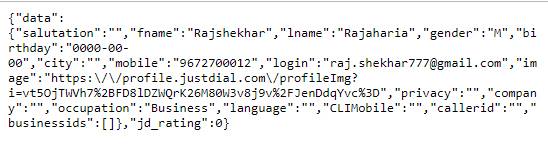
The independent security researcher, is none other than Mr.Rajasekhar Rajaharia has contacted The Hacker news and raked-off the details of how an unprotected, publicly accessible API endpoint of Justdial’s database can be accessed by anyone to view profile information over 100 million users associated with their mobile numbers. Data breach incidences in India were the second highest globally 2018, according to a report by digital security firm Gemalto.

To provide it with a proof, even verification of the API was done to check if it is ferrying details from the production server or from the backup database that might not have info belonging to the recently signed up users.
For that, a new number was given to Mr.Rajashekar and asked to call the customer care number. He neither had the JD app or used the website. He just shared haphazard details. Immediately after disconnecting the call, the profile details shared with the JD executive associate with the same phone number that was previously not found in the database, indicating that the unprotected API is pilfering real time information of users.
Although, the unprotected API is connected to the primary JD database, Rajashekhar has revealed that it’s an old API endpoint which is not currently being used by the company but left pretermitted on the server.He also told that he found this while pentesting the latest APIs in use, which are apparently protected and using authentication measures.
For now,the country does not have a provision for a user, whose data has been exposed to recover damages from companies responsible for this. A section in the draft ‘Data protection Bill’ which is undergoing consultations and pruning, however lays down directives for early disclosure of leaks and a mechanism to try cases pertaining to such lapses.







